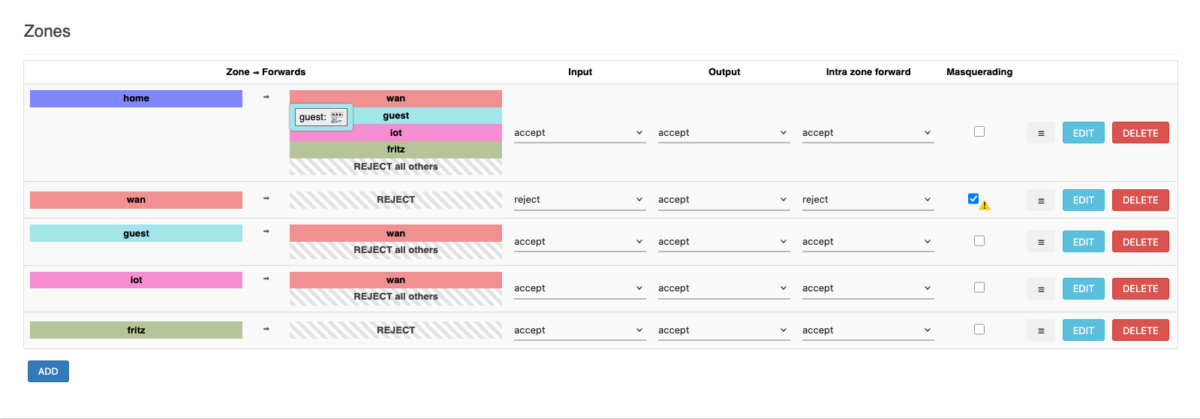
Ich habe mir vor einer Weile eine zweite Home Assistant (HA)-Instanz als “Testsystem” angelegt, um neue Integrationen, Updates, etc. zunächst gefahrlos testen zu können, ohne mein Produktivsystem zu gefährden. Dabei hatte ich ein Problem: Mein Stromzähler ist über einen Infrarot-Lesekopf und das Tool “vzlogger” an HA angebunden. vzlogger sendet die Messwerte dabei über das MQTT-Protokoll an den Broker in HA, Mosquitto. Leider kann vzlogger nur eine MQTT-Senke bedienen. Was also tun?
Ganz einfach: Es gibt bei MQTT-Brokern das Konzept der “Bridge“. Ein MQTT-Broker tritt dabei seinerseits als MQTT-Client auf, der sich gegen einen anderen MQTT-Broker verbindet. Er kann dann dorthin Nachrichten senden oder von dort empfangen. Und genau diese Konstruktion habe ich nun genutzt, um die Werte meines Stromzählers durch die Testinstanz aus der Produktivinstanz auszulesen und im Testsystem verfügbar zu machen.